Did you know how many DDoS attacks take place every day? More than 23,000 DDoS attacks were recorded every day. This translates into 16 DDoS attacks every minute, and the numbers are increasing. 2.9 million DDoS attacks were reported in the first quarter of 2021, which is 31% higher than the same period reported last year.
Even though the frequency of DDoS attacks dipped in the second quarter of 2021, experts are still predicting that the number of DDoS attacks may surge past the 12 million mark, by the end of this year. The report also brings to light an amazing fact that the size of DDoS attacks remains the same but the duration is shrinking. This is a clear indication that cyberattackers are trying to launch shorter and sophisticated DDoS attacks which can evade detection.

When it comes to industries, education and healthcare are two of the worst hit industries. Cybersecurity researchers reported a 53% increase in the number of DDoS attacks targeting healthcare facilities and a 41% increase in DDoS attacks targeting educational institutions respectively.
Want to safeguard your business from the adverse effects of DDoS attacks and ensure business continuity? This comprehensive guide will answer all the questions you might have about DDoS attacks.
- What is a DDoS Attack?
- How Does A DDoS Attack Work?
- How Long Does DDoS Attacks Last?
- How Much Does A DDoS Attack Cost?
- What is the Motivation Behind DDoS Attacks?
- What are the Different Types of DDoS Attacks?
- How To Protect Your Business Against DDoS Attacks?
- 1. Create an Incident Response Plan
- 2. Harness the Power of Cloud
- 3. Install a Web Application Firewall
- 4. Bulletproof Your Network Infrastructure
- 5. Keep an Eye Out for Red Flags
- 6. Hire a DDoS Protection Service Provider
What is a DDoS Attack?
A DDoS attack is an attempt to disrupt the normal traffic of a targeted server, website, service or network by sending a flood of malicious traffic. This overwhelms the target server and leaves it unable to handle more requests.
DDoS attacks leverage infected computers as a generator for malicious traffic. Think of a DDoS attack as a traffic jam on a highway. This prevents legitimate traffic from reaching their desired destination causing a traffic jam and delay.
How Does A DDoS Attack Work?
DDoS attacks are launched with the help of a network of compromised devices. Since these devices are already infected by malware, cyber-criminals can easily control them remotely. Individual devices are known as bots and zombies. When referred to as a group, these devices are known as a botnet.
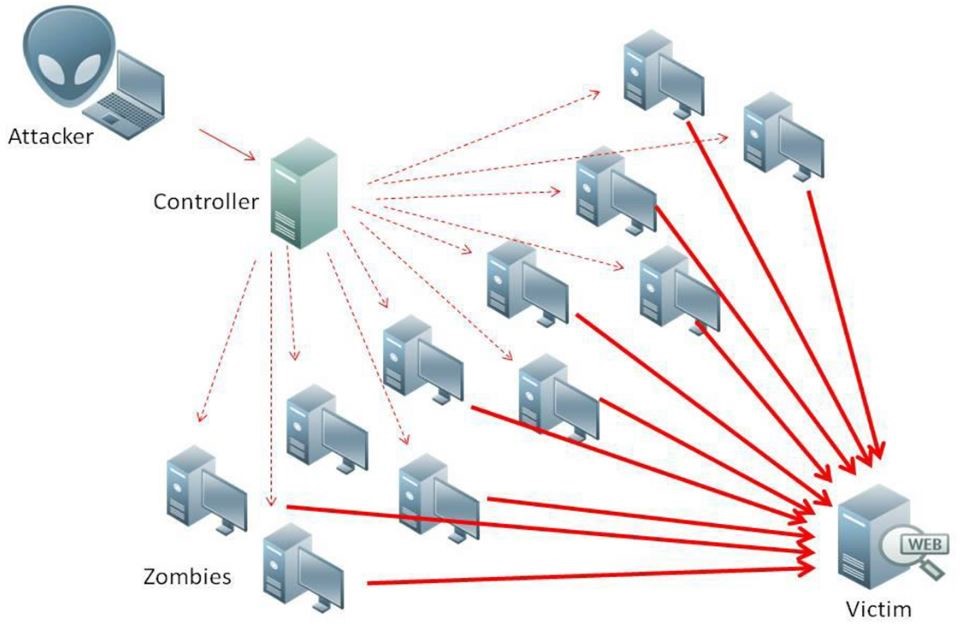
Once they have managed to compromise a group of devices, they can send remote instructions to each device. To launch an attack, every compromised device sends a request to the victim’s IP address, leaving it unable to respond to legitimate requests and causing a denial of service.
How Long Does DDoS Attacks Last?
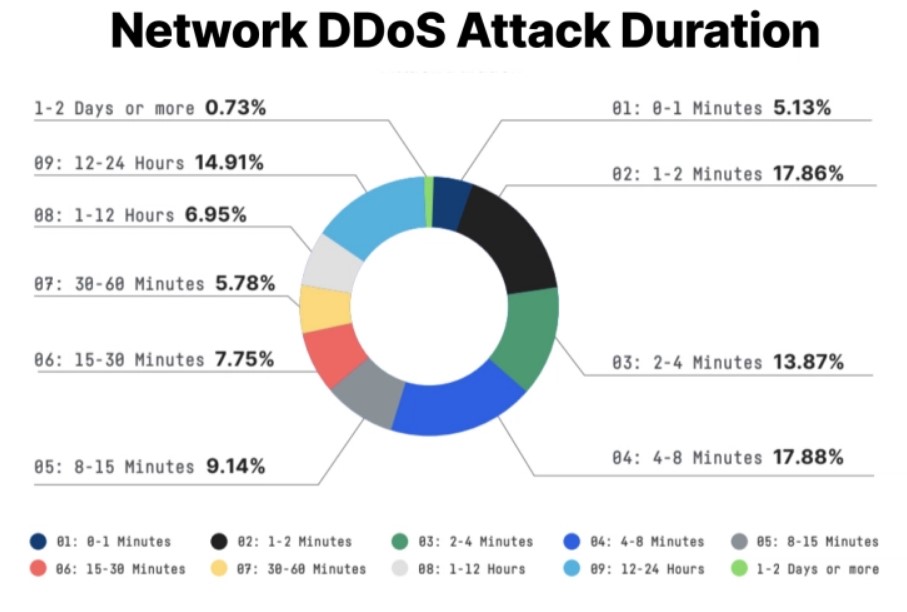
According to research, on average, a network DDoS attack only lasts 6.1 minutes, while 63.88% of network-based DDoS attacks only last for less than 15 minutes. Moreover, 14.91% of attacks in past lasted anywhere from 12 to 24 hours. Contrary to traditional beliefs, a meagre 0.73% of attacks lasted longer than a day.
How Much Does A DDoS Attack Cost?
According to DDoS cost statistics, on average, a DDoS attack can cost businesses anywhere from $20,000 to $40,000 per hour. The larger the size of the business, the higher will be the cost. According to a survey conducted by Kaspersky Labs and B2B international, the average cost of DDoS attacks for large-scale enterprises is $2 million while the average cost for small and mid-size businesses is $120,000
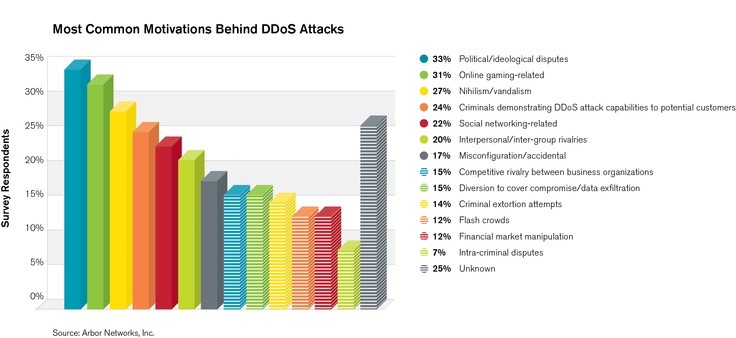
What is the Motivation Behind DDoS Attacks?
If you are wondering why cyberattackers launch DDoS attacks in the first place, here are the most common drivers:
- Ideological Disagreement
- Cyber-warfare
- Extortion
- Business Feuds
What are the Different Types of DDoS Attacks?
There are three main types of DDoS attacks
- Volume Based Attacks
- Application Layer Attacks
- Protocol Attacks
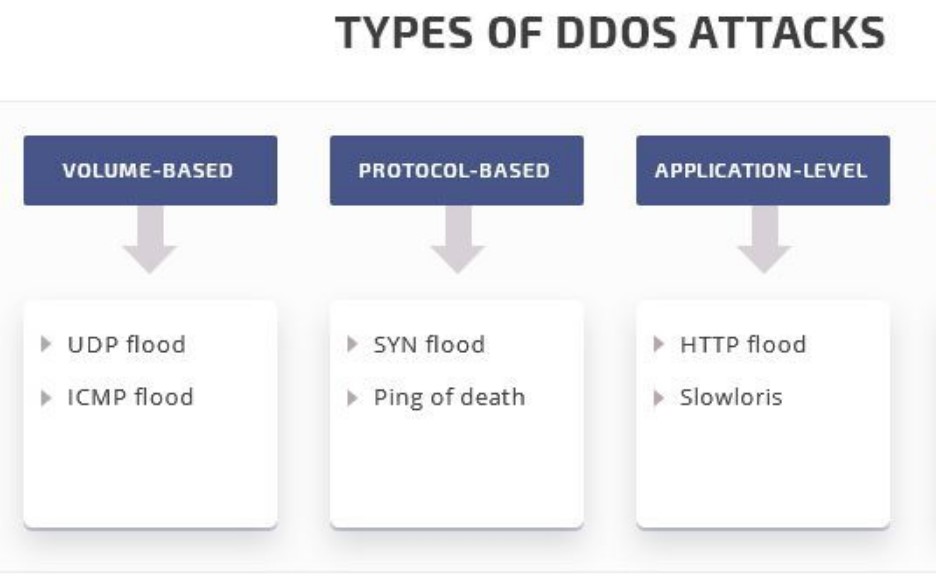
1: Volume Based Attacks
The core objective of volume-based attacks is to bombard the target site with a huge volume of illegitimate traffic and consume all its bandwidth and server capacity, leaving the servers incapable of handling other legitimate requests and traffic.
Some of the best examples of volume-based DDoS attacks are:
- UDP Floods
- ICMP Floods
- Spoofed packet floods
2: Application Layer Attacks
The primary objective of an application layer attack is to bring the server down to its knees by sending tons of seemingly innocent and legitimate requests.
Some of the best examples of application-layer attacks are:
- GET/POST Floods
- Low and Slow Attacks
- Windows, Apache and OpenBSD vulnerabilities

3: Protocol Attacks
This type of attack hijacks and consumes your server resources or firewalls or load balancers.
Some of the best examples of protocol attacks are:
- SYN Flood
- Ping of Death
- Smurf DDoS Attack
- Fragmented Packet Attacks
How To Protect Your Business Against DDoS Attacks?
Here are six ways you can prevent DDoS attacks
- Create an incident response plan
- Harness the power of cloud
- Install a web application firewall
- Bulletproof your network infrastructure
- Keep an eye out for red flags
- Hire a DDoS protection service
1. Create an Incident Response Plan
Conduct an in-depth security assessment of your organization. It will give you clarity on your current position. Once done, develop an incident response plan based on the findings of the security assessment. An incident response plan will help you combat DDoS attacks in a much better way since you will know what to do to mitigate the risk. You don’t want to be caught off-guard when a DDoS attack happens and find yourself in a conundrum. You should be ready to face the challenges posed by DDoS attacks.
2. Harness the Power of Cloud
As cloud technologies evolve and get better with time, the cloud will become more reliable and secure. Most cloud providers are also proficient at managing security issues like DDoS attacks as compared to in-house teams. When you are looking for a cloud service provider, focus on service providers that are offering DDoS protection. This not only gives you peace of mind but also reduces the burden off the shoulders of your IT team.
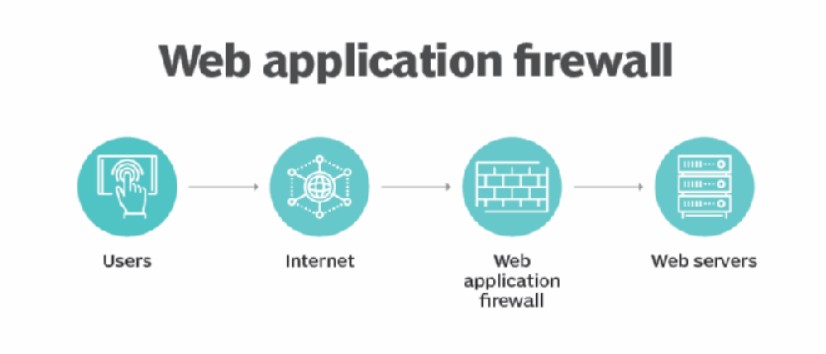
3. Install a Web Application Firewall
One of the best shields that can protect your business from DDoS attack is a web application firewall. Akin to an anti-malware and antivirus program, which protects your system from malware and viruses, a web application firewall serves as a guard that blocks malicious traffic from entering your network and damaging your web application. What’s more, a web application firewall can have a positive effect on the user experience as it also boosts the performance and responsiveness of your web application.
4. Bulletproof Your Network Infrastructure
Have you ever heard of the Tor browser? From a security standpoint, it is one of the best web browsers in the world. Do you know why? It leverages multi-layered security to keep your information private. As a result, it is harder for agencies to track you and makes it tough for cyberattackers to get past your network defenses and target your digital assets.
5. Keep an Eye Out for Red Flags
Another advantage of using multi-layered security is that it fortifies your business, but that does not mean that you can relax and overlook the security of your system. No matter how good your cybersecurity defenses might be, you must keep an eye out for red flags.
Always take a proactive approach to cybersecurity. This is when multiple layered security can protect you from different types of cybersecurity attacks. Educate your employees so they can immediately report whenever they see a warning sign,
6. Hire a DDoS Protection Service Provider
As the number of DDoS attacks grew, so did the number of service providers offering DDoS protection services. These services combine in-house, cloud and third-party resources with dedicated server hosting to provide fool-proof security.
The good news is that all the elements of your cybersecurity infrastructure comply with security standards. This makes it extremely easy for businesses to meet the compliance requirements. One of the biggest advantages of hiring a DDoS protection service is that they can deliver a fully custom-made solution catering to your specific security needs. Irrespective of how large or small your company might be, they can give you a solution that fulfills those needs in the most efficient manner.
How do you stop DDoS attacks and protect your business from them? Share it with us in the comments section below.






Add comment