In 2023, Generative AI dominated cybersecurity discussions but a data breach in ChatGPT highlighted associated risks, leading to increased focus on AI for threat detection. Ransomware surged, particularly targeting local governments, with 400 incidents in March, including a major attack on Dallas’ critical systems.
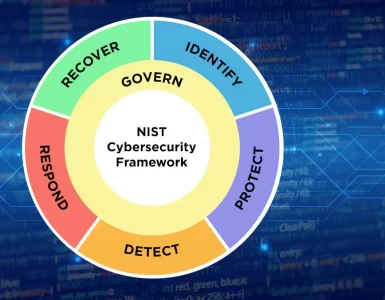
Despite these challenges, regulatory progress was made with the introduction of NIST Cybersecurity Framework 2.0 and the implementation of the White House Cybersecurity plan, aimed at fortifying protection for critical infrastructure. As organizations prepare for 2024, reflecting on these events becomes crucial for shaping effective cybersecurity strategies.
This article will highlight six cybersecurity predictions for 2024, according to IBM.
6 Cybersecurity Predictions For 2024, According to IBM
Here are six cybersecurity predictions for 2024.
1. Critical Data Protection In The Limelight
As enterprises integrate generative AI into their infrastructure, they face increased risks associated with centralized data in AI models, diverse stakeholder access, and live model usage. This risk prompts Chief Information Security Officers (CISOs) to redefine critical data that could pose an existential threat if compromised (such as fundamental intellectual property) and reassess security measures and access controls to mitigate these new challenges.
2. Generative AI Will Reshape Security Analysis
Companies have long utilized AI and machine learning to enhance the effectiveness of security technologies. In the upcoming year, the introduction of generative AI (GenAI) is set to focus on optimizing the human element of security.
Beyond automating tedious administrative tasks for security teams, GenAI will empower less experienced members to tackle more complex, higher-level responsibilities.
For instance, it will play a role in translating intricate technical content, like machine-generated log data, into simplified language, making it more understandable and actionable for novice users. This integration of generative AI into existing workflows not only streamlines current security roles but also allows security analysts to engage in more challenging tasks, thereby addressing some of the workforce and skills challenges in the security domain.
This proactive use of GenAI is expected to alleviate pressure on security teams, offering a strategic approach to managing the evolving landscape of cybersecurity threats. As generative AI takes on routine tasks and facilitates better communication through language translation, it enhances the overall efficiency and adaptability of security operations, ultimately contributing to a more resilient and responsive cybersecurity framework.
3. Rise of Harvest Now, Decrypt Later Attacks
Quantum advancements threaten widely used security protocols by the 2030s, prompting proactive efforts by organizations like NIST to develop quantum-safe cryptography standards. The U.S. The National Institute of Standards and Technology plans to publish the first set of standards in early 2024.
With the risk of “harvest now, decrypt later” attacks looming, organizations are urged to identify and transition to quantum-safe cryptography promptly. The evolving landscape necessitates early preparation for up to a 15-year transition period to ensure robust cybersecurity against quantum decryption threats. Recognizing the urgency, the World Economic Forum and National Security memorandums emphasize the need for organizations to safeguard their data and systems in light of quantum advancements.
As organizations confront the escalating risk of quantum-enabled attacks, the urgency to adopt quantum-safe cryptography is underscored by ongoing “harvest now, decrypt later” threats. With bad actors exploiting current vulnerabilities and estimates indicating a potentially lengthy transition period, organizations are encouraged to initiate the process of transitioning to quantum-safe cryptography without delay.
The proactive approach advocated by NIST emphasizes the importance of early identification of cryptographic systems in place, allowing organizations to fortify their defenses against quantum threats and ensure the long-term security of their data and systems.
4. Identity Troubles
As organizations expand their cloud services, the proliferation of disparate identity capabilities across various platforms has created a complex web of disconnected profiles. While the past strategy involved consolidating identities through a single solution, the impracticality of this approach is now recognized.
In the upcoming year, a shift towards an “identity fabric” approach is anticipated, focusing on integrating and enhancing existing identity solutions rather than replacing them. This approach aims to simplify the environment, ensuring consistent security authentication flows and improved visibility across cloud, on-premise systems, and applications.
5. AI Will Power The Next Generation of Cybersecurity Attacks
The Morris worm, considered the inaugural cyberattack in 1988, marked a seminal moment, and there are concerns about an imminent parallel in the realm of AI. As AI platforms become more accessible to businesses, there is a growing apprehension that adversaries will exploit artificial intelligence to target enterprise attack surface and to scale malicious campaigns.
Although the widespread adoption of AI in cyberattacks might not be an immediate reality, the gradual progression and testing of AI capabilities for nefarious purposes suggest that a significant event of this nature could be on the horizon.
6. Ransomware Evolution
In 2024, there is a potential recession for ransomware as an increasing number of countries pledge not to pay ransoms, and enterprises resist succumbing to the pressure of decrypting systems, opting instead to invest in rebuilding their compromised systems. This shift is causing ransomware operators to face cash flow challenges, making it difficult for them to sustain resource-intensive campaigns.
While the threat of ransomware persists, there is an anticipation of a pivot towards high-pressure data extortion attacks. Nevertheless, ransomware is expected to adapt by focusing more on consumer or small business targets, where threat actors can still maintain leverage.
The shift is likely to result in smaller ransom demands against these entities compared to larger enterprises, signaling a transformation in the landscape of ransomware attacks. Overall, the ransomware landscape is undergoing a makeover, with a shift in tactics driven by the changing dynamics of ransom payment resistance and a need for threat actors to adjust to the evolving cybersecurity environment.
Which of these cybersecurity predictions will come true in 2024? Share your thoughts with us in the comments section below.




Add comment