One type of cybersecurity attack that has been getting all the media attention lately is a ransomware attack. A flurry of ransomware attacks in the wake of the Colonial Pipeline incident might be the main reason behind its shot to fame. Ransomware attacks are nothing new and have been around for quite some time now.
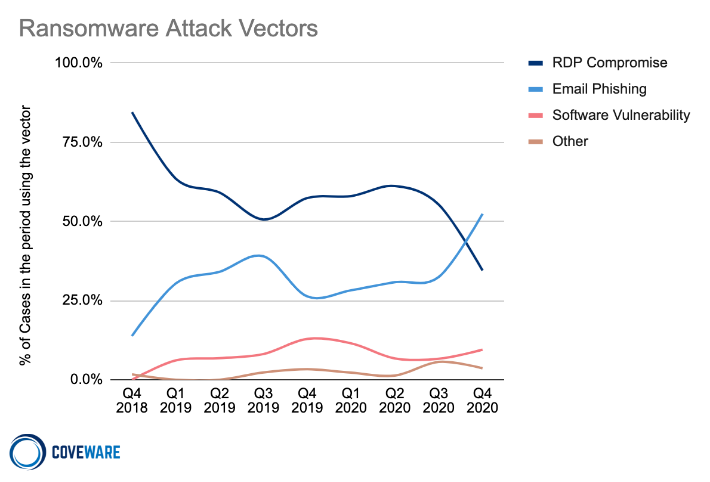
It is the financial reward of ransomware which keeps cyberattackers motivated. This is why we regularly see ransomware attacks from hacker groups. They try different tactics such as email phishing, RDP vulnerabilities and software vulnerability exploitation to make your data inaccessible. Once they succeed in fulfilling their malicious desires, they ask you to pay a ransom to get access to your data back.
Sadly, there is much more to ransomware attacks than what most people think. That is why we will bring to light some amazing facts about ransomware attacks that even IT leaders are unaware of.
Here are five facts you should know about ransomware as an IT leader.
5 Fascinating Facts About Ransomware You Wished You Knew Earlier
1. Ransomware is More Common and Effective Than You Think
Did you know that a business is targeted by ransomware attack every 11 seconds? Yes, you read that right. According to ransomware statistics, 37% of organizations became a victim of ransomware attacks last year. What’s even worse; 87% of businesses targeted by ransomware attacks in the last 12 months ended up paying the ransom. To add insult to injury, 80% of businesses who submitted the ransom payment were targeted by another ransomware attack soon after.
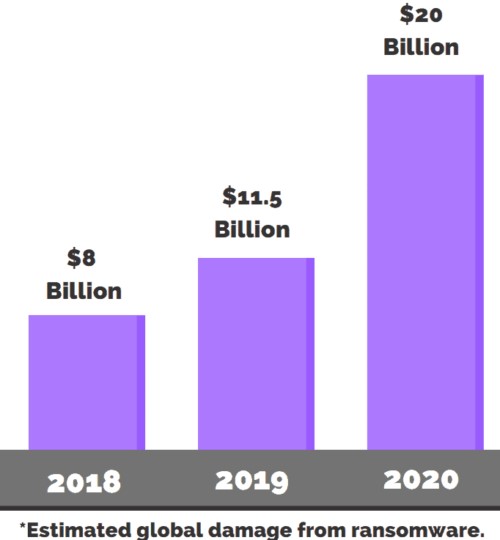
Let’s talk about the financial impact of a ransomware attack on a business. The average ransom payment request has skyrocketed from $5,000 in 2018 to $200,000 in 2020. 60% of businesses targeted by ransomware attacks reported loss of revenue while 53% said that their brand reputation took a hit.
Not only that, 29% of businesses had to lay off employees and downsize after a ransomware attack. That is how effective ransomware attacks are for cybercriminals and how devastating they are for businesses.
1. Ransomware Starts with a Phishing Attack
Most people who know cybersecurity think of ransomware attacks and phishing attacks as two different types of attacks. What they don’t know is that there is a strong connection between the two. As mentioned above, the most common tactic cyber criminals use to launch ransomware attacks is email based phishing attacks.
Hackers don’t just directly launch a ransomware attack. They first launch a phishing attack to get their foot in the door. They send phishing emails with malicious links and attachments. Hackers know that email is still being used as a formal business communication channel so they take advantage of it.
Their primary goal is to trick users into downloading those attachments or persuade them to click on these links. Once they click on the link or download the attachment, they use it as a ladder to gain access to your data, encrypt it and ask the victim to pay the ransom.
2. Ransomware Can Target Any Organization
One of the most common misconceptions businesses have about ransomware attacks is that it only targets a few industries. Sadly, that is not true. From healthcare to finance, education to law, we have already seen every industry become a target of ransomware attacks.
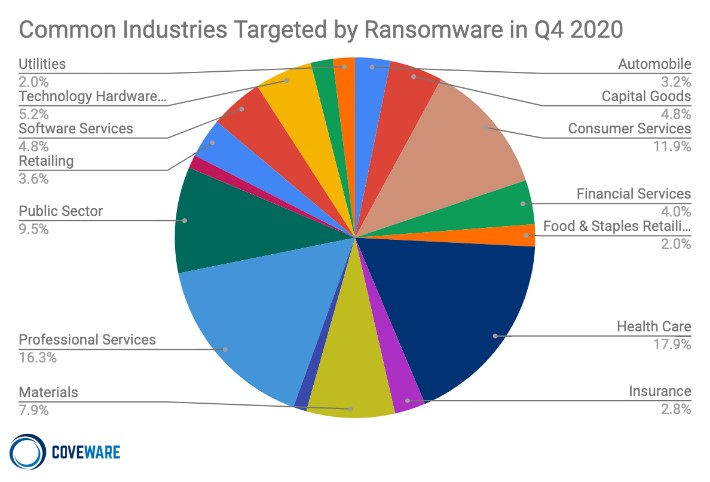
Even industries who have recently emerged on to the scene such as blockchain are not safe. What’s even more amazing is the fact that small scale businesses are as vulnerable to ransomware attack as large-scale enterprises if not more, busting the common myth that ransomware attacks only target large businesses. The threat landscape is constantly evolving and so should your cybersecurity strategy.
1. You Are as Strong as Your Weakest Link
Some businesses have a state-of-the-art security system which lulls them into a false sense of security. They think that it is impossible for cyberattackers to bypass their robust security infrastructure. What they fail to realize is that no matter how great their security systems might be, they are only as strong as the weakest link in their cybersecurity chain.
Hackers are great at finding vulnerabilities in your systems and take advantage of them. They are always on the lookout for those slight openings, which can either be a legacy system, unattended devices, or unprotected employees. Once they gain access through a single-entry point, they use it to move laterally through the network and wreak havoc on your critical IT infrastructure. This is why it is important to practice cybersecurity hygiene. Enforce cybersecurity policies that can mitigate the risk of cybersecurity attacks such as ransomware.
Brian Wilson, CISO at SAS said, “Depending on your network layout and patching posture, it takes just one instance of ransomware to potentially impact other machines on your network. Applying operating system and third-party patches or documented workarounds in a timely manner can help prevent the spread of malicious payloads throughout your network.”
2. You Can Protect Yourself from Ransomware
If you have read to this point, you might be a bit disappointed by the doom and gloom. The good news is that all hope is not lost. You can still do a lot of things to protect your business from ransomware attacks. For instance,
- Take regular backups and test your backups
- Segment your network
- Implement a robust cybersecurity framework
- Adopt a zero-trust approach
One of the main reasons why businesses have no choice but to pay the ransom is that they don’t have data backup. Make multiple copies of your data and back them up at different locations. Leverage network segmentation to prevent hackers from moving laterally through your network. Combine that with a zero-trust approach and solid cybersecurity framework and you can drastically reduce the risk of ransomware attack.
Which of these facts you didn’t know before reading this article? Share it with us in the comments section below.





Add comment