According to cyber security statistics, a ransomware attack targets a business every 11 seconds. The average downtime a company experiences after becoming a victim of a ransomware attack is three weeks which equals 21 days. What’s even worse is the fact that the average ransom demand has grown from a meager $5000 in 2018 to an astronomical $200,000 in 2020.
This makes ransomware attacks the most expensive, time consuming and frequently launched threats. Even though ransomware attacks are evolving and have started targeting critical infrastructure such as pipelines and power stations, this does not mean that businesses can afford to relax.
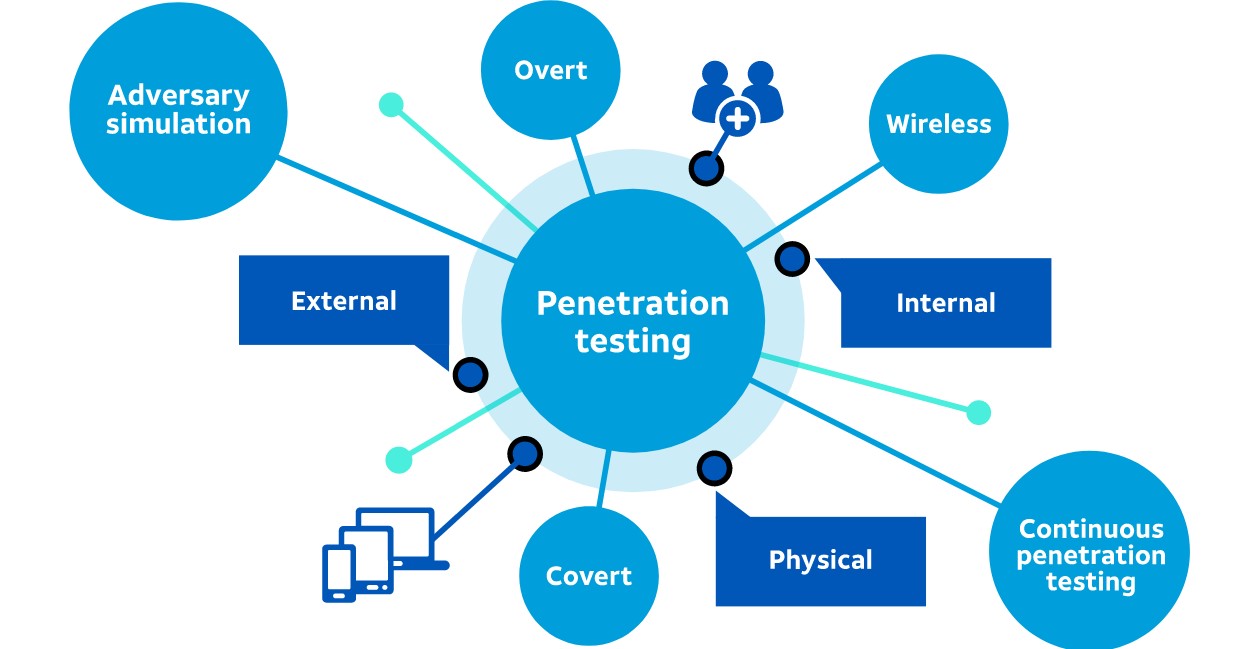
There are many ways businesses can protect themselves from ransomware attacks and one of them is penetration testing. Sadly, most businesses don’t use it as a line of defense against ransomware attacks. If you are one of those businesses, then you are at the right place.
In this article, you will learn how penetration testing can help you avert the ransomware threat.
What is Penetration Testing?
Penetration testing is the process of identifying vulnerabilities in your network and systems. It is a security practice conducted by security experts to test the strength of their cybersecurity defenses. This simulation exercise will give you a clear idea about how well your cybersecurity systems will work under an attack.
Why Penetration Testing Is Important?
Penetration testing is a great way to identify the vulnerabilities and loopholes in your current cybersecurity system. Cybersecurity professionals conducting these penetration testing exercises put themselves in the shoes of threat actors and look at the system from a hacker’s point of view. This will give you a better idea about the motivations of cyber criminals and the tools and techniques they use to target your cybersecurity systems.
With these actionable insights, you will be in a much better position to defend your business against cybersecurity attacks and data breaches. More importantly, it will help you identify vulnerabilities and fix them before they can be exploited by cyberattackers.
What are the Advantages of Penetration Testing?
Penetration testing offers many advantages to businesses. Some of them are as follows:
- Discovering vulnerabilities
With penetration testing, businesses can identify security loopholes that usually go unnoticed.
- Testing the strength of your cyber defense
Penetration testing also helps you gauge the effectiveness of your cybersecurity systems, determine the time it takes for your cybersecurity teams to mitigate threats, as well as evaluate how quickly you can find and fix vulnerabilities.
- Inspecting your firewalls
Businesses can get a better idea of how well their existing firewalls can fare against latest and current threats with the help of penetration testing. Moreover, it also gives you a clear picture about the security configurations and effectiveness of your cybersecurity policies.
- Ensure regulatory compliance
Penetration testing is also important when it comes to fulfilling regulations, meeting standards and ensuring compliance.

- Minimize downtime
Penetration testing allows your cybersecurity teams to understand how to react in crisis situations, as well as grant them a course of action on how to mitigate the risk. This drastically cuts down the downtime.
- Helps you prioritize risk
Lastly, penetration testing also assists cybersecurity teams in prioritizing risks as it provides them with a better visibility into the threat landscape. By tackling the most critical risks first and delaying the least critical ones, you can divert all your resources to the cybersecurity risk which poses the biggest threat to your business continuity.
Which Techniques Pen Testers Use?
Penetration testers will commonly use one of these three attack vectors.
- Phishing
- Remote Desktop Protocol
- Malware
How Penetration Testing Can Block Ransomware Attacks?
To understand how penetration testing helps businesses prevent ransomware attacks, you need to first understand how penetration testing methodology works.
- Planning
- Reconnaissance
- Exploitation
- Analysis
- Remediation
Let’s look at each one in detail to give you a better understanding of each phase.
- Planning
As the name suggests, pen testers create a plan, and outline the scope of the penetration tests and which attack vectors to exploit.
- Reconnaissance
In this phase, cybersecurity professionals focus on identifying the access paths attackers could use, critical assets they could target and current vulnerabilities that are already present.

- Exploitation
During the exploitation phase, penetration testers launch their attacks. In most cases, they use social engineering tactics or already known attack vectors as well as emerging attack vectors.
- Analysis
Once the attack is launched, the pen tester will create a report which describes the details about the attack and what purpose it manages to achieve. What vulnerabilities were found? How did it damage the business? Additionally, they will also include suggestions and recommendations regarding what steps businesses can take to mitigate those risks. Lastly, the report should also include advice on how an organization can improve the cybersecurity procedure.
- Remediation
Last but certainly not the least is the remediation phase where your business comes to a conclusion. During this phase, key findings from the reports are highlighted and a plan is developed to execute the findings. An action plan is also developed and executed at this phase.
Do you use penetration testing to reduce the risk of ransomware attacks? If yes, how? Let us know in the comments section below.





Add comment